This article aims to provide a framework of steps to be taken to configure a Cisco 1140 series Access Point to work as a stand alone unit that is connected to a router as a zone extender from what may or may not have an integral wireless WiFi feature – some routers do and others don’t.
This video runs through the steps to prepare for and program the AP (whilst this is a .MP4 video, some Apple browsers may be unable to decode it – I am working on making this a universally compatible video)
Just to be clear. The Cisco 114x series access points are fundamentally the same but some have two raidios and some only one. Therefore, ones with two radios, such as the AP1142 act as wireless WiFi acccess points with two SSID’s being broadcast, typically one at 2.4 GHz for legacy WiFi clients and the other at 5 GHz for the more modern devices. This article uses the AP1142 as reference.
The degree of flexibility offered by these access points is beyond the scope of this article since they ca not only act in groups, as backup units that step in – Cisco refers to this as Hot Standby, if a nearby unit fails and many other combinations of swarm like operation. Remember that these units were designed for inducstrial and commercial use cases such as shopping centres and corporate multi storey buildings spanning quite a large space.
One significant nuance that should be highlighted is that there is what is known as Autonomous Mode. This is when the unit operates independent of any controller or as part of a swarm, where it is assigned an IP address and uses that to funnel data back and forth between the two WiFi radio channels and devices connected to them and the router that it is connected to via the hard wred network port, acting as a bridge between the two ends and ultimately between users and the WWW.
CAPWAP
Cisco lightweight access points use the IETF standard Control and Provisioning of Wireless Access Points Protocol (CAPWAP) to communicate with the controller and other lightweight access points on the network.
https://www.cisco.com/c/en/us/td/docs/wireless/controller/8-6/config-guide/b_cg86/ap_connectivity_to_cisco_wlc.html
The following document is a mere chapter in one of many Cisco technical documents available to guide technicians in setting these devices up though the command line interface and Cisco IOS. Whilst it is specific, it gives an overview of the mindset of anyone considering taking on this task.
Applicaiton Specific
As referred to in the title of this article. In as far as technical configuration objective is concerned, our ultimate goal is to program our Cisco AP1142 in such a way that we can plug it into our router and power it up (details of POE routers are covered in a separate article). Resulting in two new WiFi SSID’s appearing in our airways that we can connect to.
We will be enabling AES encryption for users to connect to the WiFi Access Point using simple ASCII passwords in an effort to simplify its’ use as far as possible.
Preparation, before we begin programming
We need a computer that is running Putty Terminal Emulator. An I/O port from the computer running Putty so tht we can send and receive commnds and data to the connected Device being programmed, the AP1142.
To physcially connect our computer to the AP, we need a special cable. In our case a special Serial cable with USB connector at one end and an RJ45 connector at the other end.
We are using Windows on our laptop but this can of course be done using an Apple Mac or a computer with similar IO ports running any flavour of the Linux OS.
Due to technical reasons, Windows assigns one of 64 possible COM port identifiers to any USB Serial Port Emulator device connected to one of the laptop ports. In the old days, a computer would have one COM port and that would always be identified as COM1 but with the advent of USB serial ports, the operating system has devised a way to assigned a number after, resulting the possibility of COMx being anything from COM1, COM2, COM5, COM7 or some other COMx number.
The COMx number is important as we have to tell PuTTy which one to communicate through. Otherwise, we arae not likely to establish a link with the AP1142 that is apparently and physically connected to our laptop.
The following text document is a log of the actual configuration of our unit which was prepared as follows; We include a TEXT file of the same code as shown below..
2024 11 15 TT
Re-program Ciso1142 AP to serve as an access point - plugged into Asus RT-AC500 router
Note:----
Factory reset the AP1142 by holding reset whilst powering it on...
Background ----
After losing connection to it... The AP has been tested and is known to be working with two clients connected and using www services.
Subsequent changes----
that we have made two further updates to this configuration.
1. Added DNS 194.168.4.100 194.168.8.100 and 8.8.8.8
2. NTP (Time Server) 3.uk.pool.ntp.org
The NTP service has successfully pulled the correct time and date from the server.
Poewr on Reset -- Boot up messages -------------------
IOS Bootloader - Starting system.
FLASH CHIP: Numonyx P33
Checking for Over Erased blocks
.....................................................................
.....................................................................
.....................................................................
.......................................
Xmodem file system is available.
DDR values used from system serial eeprom.
WRDTR,CLKTR: 0x84000800, 0x40000000
RQDC, RFDC : 0x80000038, 0x0000020d
PCIE0: link is up.
PCIE0: VC0 is active
PCIE1: link is up.
PCIE1: VC0 is active
PCIEx: initialization done
flashfs[0]: 153 files, 8 directories
flashfs[0]: 0 orphaned files, 0 orphaned directories
flashfs[0]: Total bytes: 32385024
flashfs[0]: Bytes used: 8051712
flashfs[0]: Bytes available: 24333312
flashfs[0]: flashfs fsck took 22 seconds.
Reading cookie from system serial eeprom...Done
Base Ethernet MAC address: 30:e4:db:44:f8:b9
Waiting for PHY auto negotiation to complete... TIMEOUT !
Ethernet link is down.
The system has encountered an error initializing
the Ethernet port.
The system is ignoring the error and continuing to boot.
If you abort the system boot process, the following
commands will re-initialize Ethernet, TFTP, and finish
loading the operating system software:
ether_init
tftp_init
boot
button pressed for 19 seconds
process_config_recovery: set IP address and config to default 10.0.0. 1
Loading "flash:/c1140-k9w7-mx.124-25d.JA/c1140-k9w7-mx.124-25d.JA"...
#####################################################################
#####################################################################
#####################################################################
#####################################################################
#####################################################################
#####################################################################
#####################################################################
##
File "flash:/c1140-k9w7-mx.124-25d.JA/c1140-k9w7-mx.124-25d.JA"
uncom pressed and installed, entry point: 0x4000
executing...
enet halted
Restricted Rights Legend
Use, duplication, or disclosure by the Government is
subject to restrictions as set forth in subparagraph
(c) of the Commercial Computer Software - Restricted
Rights clause at FAR sec. 52.227-19 and subparagraph
(c) (1) (ii) of the Rights in Technical Data and Computer
Software clause at DFARS sec. 252.227-7013.
cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
Cisco IOS Software, C1140 Software (C1140-K9W7-M), Version 12.4(25d)J
A, RELEASE SOFTWARE (fc1)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2010 by Cisco Systems, Inc.
Compiled Thu 09-Dec-10 15:24 by prod_rel_team
Proceeding with system init
Proceeding to unmask interrupts
Initializing flashfs...
FLASH CHIP: Numonyx P33
Checking for Over Erased blocks
.....................................................................
.....................................................................
.....................................................................
.......................................
flashfs[1]: 152 files, 8 directories
flashfs[1]: 0 orphaned files, 0 orphaned directories
flashfs[1]: Total bytes: 32126976
flashfs[1]: Bytes used: 8048128
flashfs[1]: Bytes available: 24078848
flashfs[1]: flashfs fsck took 5 seconds.
flashfs[1]: Initialization complete.
flashfs[2]: 0 files, 1 directories
flashfs[2]: 0 orphaned files, 0 orphaned directories
flashfs[2]: Total bytes: 11999232
flashfs[2]: Bytes used: 1024
flashfs[2]: Bytes available: 11998208
flashfs[2]: flashfs fsck took 1 seconds.
flashfs[2]: Initialization complete....done Initializing flashfs.
Radio0 present 8363 8000 90020000 0 90030000 B
Radio1 present 8363 8000 98020000 0 98030000 0
Waiting for PHY auto negotiation to complete... TIMEOUT !
Ethernet link is down.
This product contains cryptographic features and is subject to United
States and local country laws governing import, export, transfer and
use. Delivery of Cisco cryptographic products does not imply
third-party authority to import, export, distribute or use encryption .
Importers, exporters, distributors and users are responsible for
compliance with U.S. and local country laws. By using this product you
agree to comply with applicable laws and regulations. If you are unable
to comply with U.S. and local laws, return this product immediately.
A summary of U.S. laws governing Cisco cryptographic products may be found at:
http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by sending email to
export@cisco.com.
cisco AIR-AP1142N-E-K9 (PowerPC405ex) processor (revision A0) with
98294K/32768K bytes of memory.
Processor board ID FCZ1526W4AT
PowerPC405ex CPU at 586Mhz, revision number 0x147E
Last reset from watchdog timer expired
1 Gigabit Ethernet interface
2 802.11 Radio(s)
32K bytes of flash-simulated non-volatile configuration memory.
Base ethernet MAC Address: 30:E4:DB:44:F8:B9
Part Number : 73-12836-02
PCA Assembly Number : 800-33767-02
PCA Revision Number : A0
PCB Serial Number : FOC15241CLR
Top Assembly Part Number : 800-33775-01
Top Assembly Serial Number : FCZ1526W4AT
Top Revision Number : A0
Product/Model Number : AIR-LAP1142N-E-K9
Press RETURN to get started!
*Mar 1 00:00:07.754: %SOAP_FIPS-2-SELF_TEST_IOS_SUCCESS: IOS crypto FIPS self test passed
*Mar 1 00:00:07.771: *** CRASH_LOG = YES
*Mar 1 00:00:09.056: %SOAP_FIPS-2-SELF_TEST_RAD_SUCCESS: RADIO crypto FIPS self test passed on interface Dot11Radio 0
*Mar 1 00:00:09.623: %SOAP_FIPS-2-SELF_TEST_RAD_SUCCESS: RADIO crypto FIPS self test passed on interface Dot11Radio 1Base Ethernet MAC address: 30:E4:DB:44:F8:B9
*Mar 1 00:00:50.383: %LINK-3-UPDOWN: Interface GigabitEthernet0, changed state to u ap>
ap>
*Mar 1 00:00:51.461: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEtherne t0, changed state to down
*Mar 1 00:13:40.000: %LINK-5-CHANGED: Interface Dot11Radio1, changed state to admin istratively down
*Mar 1 00:13:40.000: %LINK-5-CHANGED: Interface Dot11Radio0, changed state to admin istratively down
*Mar 1 00:13:40.002: %CDP_PD-4-POWER_OK: Full power - AC_ADAPTOR inline power sourc e
*Mar 1 00:13:40.017: %SYS-5-RESTART: System restarted --
Cisco IOS Software, C1140 Software (C1140-K9W7-M), Version 12.4(25d)JA, RELEASE SOFT WARE (fc1)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2010 by Cisco Systems, Inc.
Compiled Thu 09-Dec-10 15:24 by prod_rel_team
*Mar 1 00:13:40.017: %SNMP-5-COLDSTART: SNMP agent on host ap is undergoing a cold start
*Mar 1 00:13:40.990: %LINEPROTO-5-UPDOWN: Line protocol on Interface BVI1, changed state to up
*Mar 1 00:13:41.000: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio1, c hanged state to down
*Mar 1 00:13:41.000: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, c hanged state to down
*Mar 1 00:13:51.930: %LINK-3-UPDOWN: Interface BVI1, changed state to down
*Mar 1 00:13:52.930: %LINEPROTO-5-UPDOWN: Line protocol on Interface BVI1, changed state to down
ap>
ap>
ap>
ap>enable
Password:
ap#
ap#
ap#conf term
Enter configuration commands, one per line. End with CNTL/Z.
ap(config)#
ap(config)#exit
ap#
ap#
ap#?
Exec commands:
access-enable Create a temporary Access-List entry
access-template Create a temporary Access-List entry
archive manage archive files
cd Change current directory
clear Reset functions
clock Manage the system clock
configure Enter configuration mode
connect Open a terminal connection
copy Copy from one file to another
crypto Encryption related commands.
debug Debugging functions (see also 'undebug')
delete Delete a file
dir List files on a filesystem
disable Turn off privileged commands
disconnect Disconnect an existing network connection
dot11 IEEE 802.11 commands
dot1x IEEE 802.1X Exec Commands
enable Turn on privileged commands
erase Erase a filesystem
exit Exit from the EXEC
format Format a filesystem
fsck Fsck a filesystem
help Description of the interactive help system
led LED functions
lock Lock the terminal
login Log in as a particular user
logout Exit from the EXEC
mkdir Create new directory
monitor Monitoring different system events
more Display the contents of a file
name-connection Name an existing network connection
no Disable debugging functions
ping Send echo messages
pwd Display current working directory
radius radius exec commands
release Release a resource
reload Halt and perform a cold restart
rename Rename a file
renew Renew a resource
resume Resume an active network connection
rmdir Remove existing directory
rsh Execute a remote command
send Send a message to other tty lines
set Set system parameter (not config)
show Show running system information
ap#
ap#
ap#
ap#
ap#show ?
aaa Show AAA values
access-expression List access expression
access-lists List access lists
accounting Accounting data for active sessions
aliases Display alias commands
archive Archive of the running configuration information
arp ARP table
auto Show Automation Template
boot show boot attributes
bridge Bridge Forwarding/Filtering Database [verbose]
buffers Buffer pool statistics
call Show call
caller Display information about dialup connections
cca CCA information
cdp CDP information
class-map Show QoS Class Map
clock Display the system clock
configuration Configuration details
controllers Interface controller status
crypto Encryption module
dampening Display dampening information
data-corruption Show data errors
debugging State of each debugging option
derived-config Derived operating configuration
dhcp Dynamic Host Configuration Protocol status
dot11 IEEE 802.11 show information
dot1x Dot1x information
eap Shows EAP registration/session information
event-manager Event manager information
exception exception information
file Show filesystem information
flash: display information about flash: file system
hardware Hardware specific information
history Display the session command history
hosts IP domain-name, lookup style, nameservers, and host table
html HTML helper commands
iapp DDP IAPP
idb List of Interface Descriptor Blocks
interfaces Interface status and configuration
inventory Show the physical inventory
ip IP information
led LED functions
line TTY line information
location Display the system location
logging Show the contents of logging buffers
ap#
ap#show dot11 ?
aaa Authentication, Authorization, and Accounting
activity-timeout Default/Maximum activity timeout values
adjacent-ap Display Fast Secure Roaming adjacent AP list
antenna-alignment Display recent antenna alignment results
arp-cache Arp Cache
associations association information
bssid show SSID to BSSID mapping
cac Admission Control Statistics
carrier Display recent carrier test results
directed-roam Directed Roaming Clients/APs
ids Intrusion Detection System
lbs Display LBS configuration and status
linktest Display recent linktest results
mac-authen MAC authentication details
network-map Network Map
statistics statistics information
traffic-streams Admitted WMM Traffic-Streams
vlan-name Display VLAN name to ID map(s)
ap#
ap#show dot11 network-map
network-map is disabled
ap#
ap#
ap#show dot11 mac-authen ?
filter-cache MAC filter cache
ap#
ap#show dot11 mac-authen filter-cache ?
H.H.H MAC Address
| Output modifiers
<cr>
ap#show dot11 mac-authen filter-cache
ap#
ap#
ap#
ap#
ap#show dot11 bssid
ap#show
ap#show ?
aaa Show AAA values
access-expression List access expression
access-lists List access lists
accounting Accounting data for active sessions
aliases Display alias commands
archive Archive of the running configuration information
arp ARP table
auto Show Automation Template
boot show boot attributes
bridge Bridge Forwarding/Filtering Database [verbose]
buffers Buffer pool statistics
call Show call
caller Display information about dialup connections
cca CCA information
cdp CDP information
class-map Show QoS Class Map
clock Display the system clock
configuration Configuration details
controllers Interface controller status
crypto Encryption module
dampening Display dampening information
data-corruption Show data errors
ap#show arp
ap#
ap#show buffers
Buffer elements:
1119 in free list (1119 max allowed)
28 hits, 0 misses, 619 created
Public buffer pools:
Small buffers, 104 bytes (total 128, permanent 128):
128 in free list (20 min, 256 max allowed)
21 hits, 0 misses, 0 trims, 0 created
0 failures (0 no memory)
Middle buffers, 600 bytes (total 128, permanent 128):
128 in free list (10 min, 256 max allowed)
25 hits, 0 misses, 0 trims, 0 created
0 failures (0 no memory)
Big buffers, 1536 bytes (total 128, permanent 128):
128 in free list (5 min, 256 max allowed)
28 hits, 0 misses, 0 trims, 0 created
0 failures (0 no memory)
VeryBig buffers, 4520 bytes (total 256, permanent 256):
256 in free list (0 min, 256 max allowed)
0 hits, 0 misses, 0 trims, 0 created
0 failures (0 no memory)
Large buffers, 5024 bytes (total 0, permanent 0):
0 in free list (0 min, 5 max allowed)
0 hits, 0 misses, 0 trims, 0 created
0 failures (0 no memory)
Huge buffers, 18024 bytes (total 0, permanent 0):
0 in free list (0 min, 2 max allowed)
0 hits, 0 misses, 0 trims, 0 created
0 failures (0 no memory)
Interface buffer pools:
Wlan Pool buffers, 2500 bytes (total 1677, permanent 1677):
711 in free list (0 min, 1677 max allowed)
966 hits, 0 fallbacks
838 max cache size, 584 in cache
254 hits in cache, 0 misses in cache
Header pools:
ap#
-----------------------------------------------------------------------------
ap#
ap#show running-config
Building configuration...
Current configuration : 1414 bytes
!
version 12.4
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
service password-encryption
!
hostname ap
!
logging rate-limit console 9
enable secret 5 $1$FYpa$ES9qiBGVJvx5vzMhEWIOk0
!
no aaa new-model
!
!
dot11 syslog
!
!
username Cisco password 7 02250D480809
!
!
bridge irb
!
!
interface Dot11Radio0
no ip address
no ip route-cache
shutdown
antenna gain 0
station-role root
bridge-group 1
bridge-group 1 subscriber-loop-control
bridge-group 1 block-unknown-source
no bridge-group 1 source-learning
no bridge-group 1 unicast-flooding
bridge-group 1 spanning-disabled
!
interface Dot11Radio1
no ip address
no ip route-cache
shutdown
antenna gain 0
no dfs band block
channel dfs
station-role root
bridge-group 1
bridge-group 1 subscriber-loop-control
bridge-group 1 block-unknown-source
no bridge-group 1 source-learning
no bridge-group 1 unicast-flooding
bridge-group 1 spanning-disabled
!
interface GigabitEthernet0
no ip address
no ip route-cache
duplex auto
speed auto
no keepalive
bridge-group 1
no bridge-group 1 source-learning
bridge-group 1 spanning-disabled
!
interface BVI1
ip address dhcp client-id GigabitEthernet0
no ip route-cache
!
ip http server
no ip http secure-server
ip http help-path http://www.cisco.com/warp/public/779/smbiz/prodconfig/help/eag
bridge 1 route ip
!
!
!
line con 0
line vty 0 4
login local
!
end
-----------------------------------------------------------------------------
CONFIGURE BV1 (the Bridge interface)
-----------------------------------------------------------------------------
ap#
ap#enable
ap#conf term
Enter configuration commands, one per line. End with CNTL/Z.
ap(config)#
ap(config)#
ap(config)#
ap(config)#int bv1
ap(config-if)#ip address 192.168.1.200 255.255.255.0
ap(config-if)#
ap(config-if)#exit
ap(config)#ip default-gateway 192.168.1.1
ap(config)#
ap(config)#dot11 ssid Cisco_AP
ap(config-ssid)#
ap(config-ssid)#auth open
ap(config-ssid)#auth key wpa v 2
ap(config-ssid)#
ap(config-ssid)#wpa-psk ascii abc123ABC123
ap(config-ssid)#guest-mode
ap(config-ssid)#exit
-----------------------------------------------------------------------------
CONFIGURE d0 Dot11 Radio 0, The 2.4GHz Wifi radio
-----------------------------------------------------------------------------
ap(config)#
ap(config)#
ap(config)#int d0
ap(config-if)#encryption mode ciphers aes
ap(config-if)#ssid Cisco_AP
ap(config-if)#channel 1
ap(config-if)#no shutdown
ap(config-if)#
*Mar 1 00:31:25.141: %LINK-5-CHANGED: Interface Dot11Radio0, changed state to reset
ap(config-if)#
*Mar 1 00:31:25.149: %LINK-3-UPDOWN: Interface Dot11Radio0, changed state to up
*Mar 1 00:31:26.148: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to up
*Mar 1 00:31:31.929: %LINK-3-UPDOWN: Interface BVI1, changed state to up
*Mar 1 00:31:32.929: %LINEPROTO-5-UPDOWN: Line protocol on Interface BVI1, changed state to up
ap(config-if)#
ap(config-if)#
ap(config-if)#exit
ap(config)#
ap(config)#
ap(config)#
ap(config)#
ap(config)#dot11 ssid Cisco_AP 5GHz
ap(config-ssid)#
ap(config-ssid)#
ap(config-ssid)#auth open
ap(config-ssid)#auth key wpa ver 2
ap(config-ssid)#wpa-psk ascii abc123ABC123
ap(config-ssid)#guest-mode
ap(config-ssid)#exit
ap(config)#
ap(config)#
ap(config)#
-----------------------------------------------------------------------------
CONFIGURE d0 Dot11 Radio 1, The 5GHz Wifi radio
-----------------------------------------------------------------------------
ap(config)#
ap(config)#int d1
ap(config-if)#encryption mode ciphers aes
ap(config-if)#ssid Cisco_AP 5GHz
ap(config-if)#no shutdown
ap(config-if)#
*Mar 1 00:33:49.998: %LINK-5-CHANGED: Interface Dot11Radio1, changed state to reset
*Mar 1 00:33:53.623: %DOT11-6-DFS_SCAN_START: DFS: Scanning frequency 5560 MHz for 60 seconds.
*Mar 1 00:33:53.623: %DOT11-6-FREQ_USED: Interface Dot11Radio1, frequency 5560 selected
*Mar 1 00:33:53.623: %LINK-3-UPDOWN: Interface Dot11Radio1, changed state to up
*Mar 1 00:33:54.623: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio1, changed state to up
ap(config-if)#
ap(config-if)#
ap(config-if)#channel ?
<36-5700> One of: 36 40 44 48 52 56 60 64 100 104 108 112 116 132 136 140
5180 5200 5220 5240 5260 5280 5300 5320 5500 5520 5540 5560 5580
5660 5680 5700
dfs Use Dynamic Frequency Selection
width Bandwidth used
ap(config-if)#channel 36
ap(config-if)#
*Mar 1 00:34:27.229: %LINK-5-CHANGED: Interface Dot11Radio1, changed state to reset
*Mar 1 00:34:27.242: %LINK-3-UPDOWN: Interface Dot11Radio1, changed state to up
ap(config-if)#
ap(config-if)#
ap(config-if)#exit
ap(config)#
ap(config)#
ap(config)#exit
ap#
*Mar 1 00:34:59.025: %SYS-5-CONFIG_I: Configured from console by console
-----------------------------------------------------------------------------
BACKUP THIS CONFIGURATION TO 'StartUp-Configuration'
-----------------------------------------------------------------------------
ap#
ap#copy run start
Destination filename [startup-config]?
Building configuration...
[OK]
ap#
ap#configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
ap(config)#int d1
ap(config-if)#
ap(config-if)#do copy run start
Destination filename [startup-config]?
Building configuration...
[OK]
ap(config-if)#exit
ap(config)#exit
ap#
ap#
ap#
ap#
*Mar 1 00:38:05.897: %SYS-5-CONFIG_I: Configured from console by console
ap#
ap#show dot11 bssid
Interface BSSID Guest SSID
Dot11Radio1 b862.1f28.1dd0 Yes Cisco_AP 5GHz
Dot11Radio0 b862.1f16.ed30 Yes Cisco_AP
ap#
ap#show
ap#show ?
aaa Show AAA values
access-expression List access expression
access-lists List access lists
accounting Accounting data for active sessions
aliases Display alias commands
archive Archive of the running configuration information
arp ARP table
auto Show Automation Template
boot show boot attributes
bridge Bridge Forwarding/Filtering Database [verbose]
buffers Buffer pool statistics
call Show call
caller Display information about dialup connections
cca CCA information
cdp CDP information
class-map Show QoS Class Map
clock Display the system clock
configuration Configuration details
controllers Interface controller status
crypto Encryption module
dampening Display dampening information
data-corruption Show data errors
debugging State of each debugging option
derived-config Derived operating configuration
dhcp Dynamic Host Configuration Protocol status
dot11 IEEE 802.11 show information
dot1x Dot1x information
eap Shows EAP registration/session information
event-manager Event manager information
exception exception information
file Show filesystem information
flash: display information about flash: file system
hardware Hardware specific information
history Display the session command history
hosts IP domain-name, lookup style, nameservers, and host table
html HTML helper commands
iapp DDP IAPP
idb List of Interface Descriptor Blocks
interfaces Interface status and configuration
inventory Show the physical inventory
ip IP information
led LED functions
line TTY line information
location Display the system location
logging Show the contents of logging buffers
login Display Secure Login Configurations and State
memory Memory statistics
monitor Monitoring different system events
parser Display parser information
policy-manager Policy Manager
policy-map Show QoS Policy Map
privilege Show current privilege level
processes Active process statistics
profile SOAP profile functions
radius Shows radius information
ram: display information about ram: file system
region Region Manager Status
registry Function registry information
reload Scheduled reload information
resource Display Resource Usage/Relations and more details
rhosts Remote-host+user equivalences
rmi Resource User Infrastructure information
running-config Current operating configuration
sessions Information about Telnet connections
smf Software MAC filter
snmp snmp statistics
sntp Simple network time protocol
spanning-tree Spanning tree topology
spectrum Spectrum FW show commands
ssh Status of SSH server connections
ssl Show SSL command
stacks Process stack utilization
startup-config Contents of startup configuration
subscriber-policy Subscriber policy
subsys Show subsystem information
table-map Show Table Map
tacacs Shows tacacs+ server statistics
tcp Status of TCP connections
tech-support Show system information for Tech-Support
template Template information
terminal Display terminal configuration parameters
time-range Time range
trace trace information
tunnel Show configured tunnels
users Display information about terminal lines
version System hardware and software status
vlans Virtual LANs Information
wlccp WLCCP info
ap#show host
ap#show hosts ?
WORD Hostname for specific information
| Output modifiers
<cr>
ap#show hosts
Default domain is not set
Name/address lookup uses domain service
Name servers are 255.255.255.255
Codes: UN - unknown, EX - expired, OK - OK, ?? - revalidate
temp - temporary, perm - permanent
NA - Not Applicable None - Not defined
Host Port Flags Age Type Address(es)
ap#
ap#
ap#
ap#
ap#
ap#
ap#conf term
ap#conf terminal
Enter configuration commands, one per line. End with CNTL/Z.
ap(config)#?
Configure commands:
aaa Authentication, Authorization and Accounting.
access-list Add an access list entry
alias Create command alias
archive Archive the configuration
arp Set a static ARP entry
banner Define a login banner
boot Boot Commands
bridge Bridge Group.
buffers Adjust system buffer pool parameters
call Configure Call parameters
cdp Global CDP configuration subcommands
class-map Configure QoS Class Map
clock Configure time-of-day clock
configuration Configuration access
crypto Encryption module
default Set a command to its defaults
default-value Default character-bits values
define interface range macro definition
do To run exec commands in config mode
dot11 IEEE 802.11 config commands
dot1x IEEE 802.1X Global Configuration Commands
ap(config)#clock
ap(config)#clock ?
initialize Initialize system clock on restart
save backup of clock with NVRAM
summer-time Configure summer (daylight savings) time
timezone Configure time zone
ap(config)#se
ap(config)#se?
service
ap(config)#co
ap(config)#configuration ?
mode Configuration mode
ap(config)#configuration moded ?
% Unrecognized command
ap(config)#configuration mode
ap(config)#configuration mode ?
exclusive Configuration mode exclusive
ap(config)#configuration mode ex
ap(config)#configuration mode exclusive ?
auto Lock configuration mode automatically
manual Lock configuration mode on-demand
ap(config)#copy
ap(config)#copy ru
ap(config)#exit
ap#
ap#
ap#co
*Mar 1 00:47:54.276: %SYS-5-CONFIG_I: Configured from console by conso
ap#
ap#cop
ap#copy run
ap#copy running-config st
ap#copy running-config startup-config
Destination filename [startup-config]?
Building configuration...
[OK]
ap#copy run
ap#
Verifying the results
Once programmedd, we detch the unit from thr laptop and plug it back in on the ceiling, where it will live to serve its’ purpose and powered from a Cisco SG-200 Switch with POE out put and so, no external power is needed to power our AP1142.
Since our laptop is on the same network, we fire up our browser and type in the IP address of the access-point, which is 192.168.1.200 Here’s the ‘home page’ of the AP.
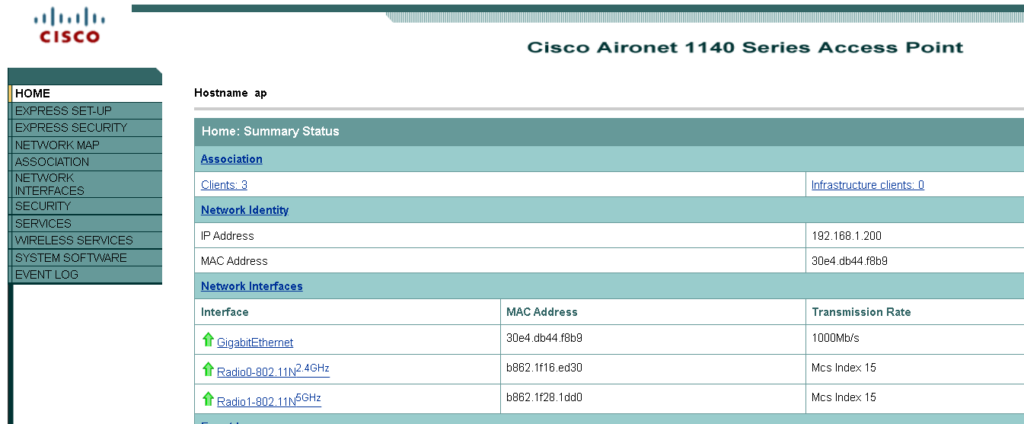
We can see a brief summary of number of cliets currently connected, network information and a list of the three Network Interfaces; That is a GigabitEthernet port (connected to our Router [via the POE Switch])… and the Radio0-802.11N 2.4GHz and Radio0-802.11N 5GHz, each with unique MAC address.
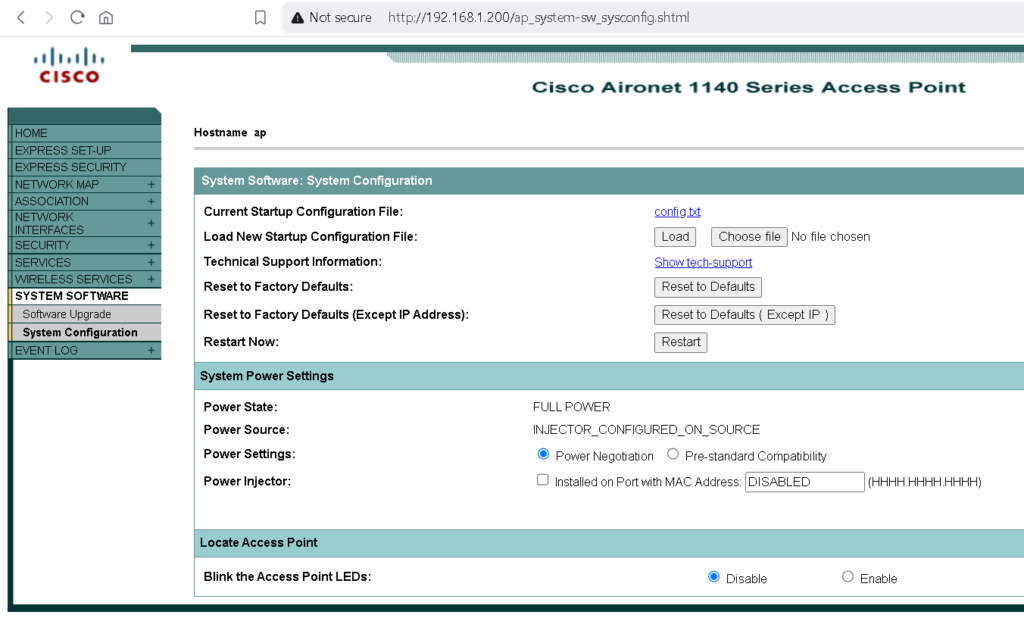
Using the menu on the left hand side of the screen and navigating to the SYSTEM SOFTWARE page, we can see a number of options including Configuration files and option to load a New Startup Configuration File as well as several buttons to Reset and Restart the AP.
We can also see the Power State and the source of as eing INJECTOR_CONFIGURE_ON_SOURCE meaning it is integral to the RJ45 Gigabit interface.
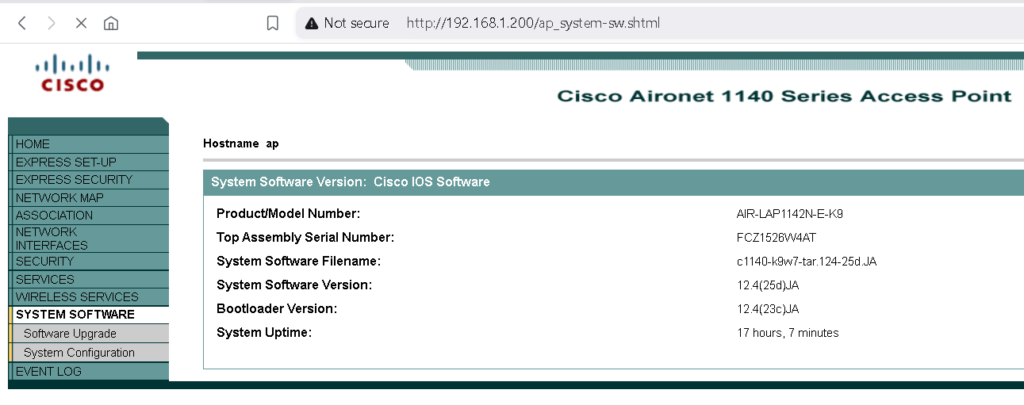
And finally, the following image shows the current running firmware and version that is running on this AP as well as system Up-Time since last power-cycle.
We include the StartUp-Configuration file downloaded from the web-interface shown below and include the confi.txt file here for further study.
In this article we have shown how a commercial access point can be adopted to work in our home environment and how to adapt it for this purpose. We have configured this AP to be a part of our home-network by assigning it and IP address and setting p the three interfaces, one of which is running on POE Switch and two Radios to facilititate 2.4 and 5 GHz connection channels.
We have also taken a brief look at the web-user interface, where further optimizations and customizations can be made as well as monitoring usage and statistics on data flowing through the access-point.
Topics for further discussion
We have found that there are plenty of these units available for sale in market places like eBay and Amazon because Cisco has obviously rolledd out up to date technologies and better performance equivalanets. However, in our opinion, these ‘commercial grae’ access points are adequate for home or small business use, such as public houseses where WiFi extenders are desirable. As long as we know how to adapt and programe these, there is no reason why they should not be recycled given that their coverage and dedsignedd for large number of simulataneous connections are going to be better than most personal equipment available to us.
As we have highlighted at the beginning of this article, we have setup our Cisco AP112 in Autonomous Mode, as opposed to CAPWAP, which inherently is intended to work as part of swarms of APs and accordingly are managedd from a further separate piece of IT equipment referred to as a Controller. The CAPWAP and Autonomous vairants rely on fundamentally different firmware versions and it is not very clear from their physical appearance which they might be. Therefore, if we end up with the wrong firmware, it is necessary to re-flash with the correct firmware before we can transform it into an Autonomous unit. This transformation will be the subject of our next article as we investigate and convert one as soon as we can get hold of a copy of the Autnomous variant of the firmware needed to do this.